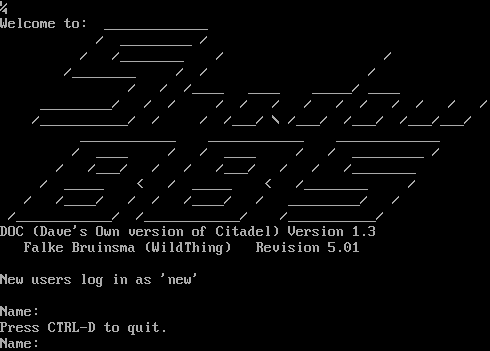
shadowbbs.com:23
Connection Banner:
Server URLs
- Telnet: shadowbbs.com:23
- Website: http://shadowbbs.com
Server Location: 🇺🇸 United States (GeoIP)
Listing
BBS Name: Shadow BBS (from listing)
Listed Location: Glendale Heights, IL, USA
BBS Software
Detected: Citadel
Encoding
Effective encoding: cp437
Override: cp437 (from bbslist.txt)
Scanner detected: cp437
Telnet Fingerprint
This fingerprint is shared by 3 other servers.
Options offered by server: ECHO, SGA
Options requested from client: NAWS
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "cdbdaaf8df581f5c",
"fingerprint-data": {
"offered-options": [
"ECHO",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"NAWS"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\n\r\nPress CTRL-D to quit.\r\nName: ",
"banner_before_return": "\u00bc\r\nWelcome to: _____________\r\n / _________ /\r\n / /________ / /\r\n /________ / / /\r\n / / /____ ____ _____/ ____\r\n _________/ / / / / / / / / / / / /\r\n /___________/ / / /___/ \\ /___/ /___/ /___/___/\r\n ____________ ____________ _____________\r\n / ____ / / ____ / / _________ /\r\n / /___/ / / /___/ / / /________ \r\n / _____ < / _____ < /________ / \r\n / /____/ / / /____/ / _________/ / \r\n /____________/ /____________/ /___________/ \r\nDOC (Dave's Own version of Citadel) Version 1.3 \r\n Falke Bruinsma (WildThing) Revision 5.01\r\n \r\nNew users log in as 'new'\r\n\r\nName: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "cp437",
"option_states": {
"server_offered": {
"ECHO": true,
"SGA": true
},
"server_requested": {
"0x24": false,
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"NAWS": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5148990154266357,
"total": 11.08048391342163
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:22:34.089487+00:00",
"host": "shadowbbs.com",
"ip": "135.233.115.198",
"port": 23
},
{
"connected": "2026-04-05T18:58:55.709422+00:00",
"host": "shadowbbs.com",
"ip": "135.233.115.198",
"port": 23
},
{
"connected": "2026-04-07T06:22:26.837634+00:00",
"host": "shadowbbs.com",
"ip": "135.233.115.198",
"port": 23
},
{
"connected": "2026-04-10T00:34:20.458949+00:00",
"host": "shadowbbs.com",
"ip": "135.233.115.198",
"port": 23
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug shadowbbs.com 23
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=shadowbbs.com port=23
INFO client_base.py:188 Connected to <Peer 135.233.115.198 23>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:732 IAC b'\xac': not a legal 2-byte cmd, treating as data
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:789 WILL SGA unsolicited
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:789 WILL ECHO unsolicited
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC DO NAWS
DEBUG stream_writer.py:1887 handle_do(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = True
DEBUG stream_writer.py:1024 send IAC WILL NAWS
DEBUG stream_writer.py:2507 send IAC SB NAWS (rows=25, cols=80) IAC SE
DEBUG stream_writer.py:3384 local_option[NAWS] = True
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:773 recv IAC DO b'$'
DEBUG stream_writer.py:1887 handle_do(b'$')
DEBUG stream_writer.py:1995 DO b'$' not supported.
DEBUG stream_writer.py:3384 local_option[b'$'] = False
DEBUG stream_writer.py:1024 send IAC WONT b'$'
DEBUG client_base.py:513 negotiation failed after 4.00s.
DEBUG client_base.py:519 failed-reply: 'WILL ZMP, WILL AARDWOLF, WILL MSDP, WILL GMCP, WILL MXP, WILL ATCP, WILL MSSP, WILL MSP,
WILL MCCP2_COMPRESS, WILL MCCP3_COMPRESS, DO ZMP, DO AARDWOLF, DO MSDP, DO GMCP, DO MXP, DO ATCP, DO MSSP, DO MSP, DO
MCCP2_COMPRESS, DO MCCP3_COMPRESS'
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT b'$'
DEBUG stream_writer.py:2010 handle_dont(b'$')
DEBUG stream_writer.py:3384 pending_option[WILL + b'$'] = False
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:844 connection for server fingerprint cdbdaaf8df581f5c
INFO client_base.py:120 Connection closed to <Peer 135.233.115.198 23>