pool-74-104-122-212.bstnma.fios.verizon.net:23
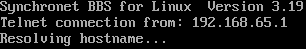
Connection Banner:
Server URLs
Server Location: 🇺🇸 United States (GeoIP)
BBS Software
Detected: Synchronet
Encoding
Effective encoding: ascii
Scanner detected: ascii
Telnet Fingerprint
This fingerprint is shared by 8 other servers.
Options offered by server: AARDWOLF, ATCP, GMCP, MCCP2, MCCP3, MSDP, MSP, MSSP, MXP, ZMP
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "46cf87861dca7460",
"fingerprint-data": {
"offered-options": [
"AARDWOLF",
"ATCP",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"ZMP"
],
"probed-protocol": "server",
"refused-options": [
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"SGA",
"STATUS"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\r\nSynchronet BBS for Linux Version 3.19\r\nTelnet connection from: 192.168.65.1\r\nResolving hostname...\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"AARDWOLF": true,
"ATCP": true,
"GMCP": true,
"MCCP2": true,
"MCCP3": true,
"MSDP": true,
"MSP": true,
"MSSP": true,
"MXP": true,
"ZMP": true
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5207035541534424,
"total": 11.032992124557495
}
}
},
"sessions": [
{
"connected": "2026-04-05T19:30:41.591254+00:00",
"host": "pool-74-104-122-212.bstnma.fios.verizon.net",
"ip": "74.104.122.212",
"port": 23
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug pool-74-104-122-212.bstnma.fios.verizon.net 23
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=pool-74-104-122-212.bstnma.fios.verizon.net port=23
ERROR client.py:1318 pool-74-104-122-212.bstnma.fios.verizon.net:23: [Errno 111] Connect call failed ('74.104.122.212', 23)