95.165.2.26 (technotron.asuscomm.com)
technotron.asuscomm.com:23
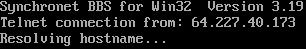
Connection Banner:
This banner is more than 98% similar to 4 other servers:
🇺🇸 tmzbbs01.synchro.net:23 (99% match)
🇦🇺 bbs.ninthchevron.com.au:23 (98% match)
🇳🇱 bookworm.synchro.net:2323 (98% match)
🇺🇸 jamesmauler.net:23 (98% match)
Server URLs
- RLogin: technotron.asuscomm.com:23
- FTP: ftp://technotron.asuscomm.com
- Secure WebSocket: wss://technotron.asuscomm.com:11235
- WebSocket: ws://technotron.asuscomm.com:1123
- Website: http://technotron.asuscomm.com
Server Location: 🇷🇺 Russia (GeoIP)
Listing
BBS Name: Antikitera (from listing)
Listed Location: Trekgorka, , Russia
BBS Software
Detected: Synchronet
Encoding
Effective encoding: ascii
Scanner detected: cp437
Telnet Fingerprint
This fingerprint is shared by 132 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "",
"banner_before_return": "\r\nSynchronet BBS for Win32 Version 3.19\r\nTelnet connection from: 64.227.40.173\r\nResolving hostname...",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "cp437",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5131213665008545,
"total": 11.028822183609009
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:10:07.149148+00:00",
"host": "technotron.asuscomm.com",
"ip": "95.165.2.26",
"port": 23
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug technotron.asuscomm.com 23
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=technotron.asuscomm.com port=23
ERROR client.py:1318 technotron.asuscomm.com:23: TCP connection to technotron.asuscomm.com:23 timed out after 30.0s
technotron.asuscomm.com:3261
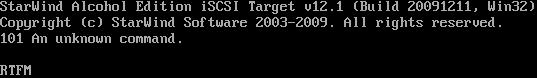
Connection Banner:
Server URLs
- RLogin: technotron.asuscomm.com:3261
Server Location: 🇷🇺 Russia (GeoIP)
BBS Software
Reported: Synchronet
Encoding
Effective encoding: ascii
Scanner detected: ascii
Telnet Fingerprint
This fingerprint is shared by 132 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "e89ffa4fe5c32389",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"ECHO",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"SGA",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "101 An unknown command.\r\n\r\nRTFM\r\n\r\n",
"banner_before_return": "\u001b[2JStarWind Alcohol Edition iSCSI Target v12.1 (Build 20091211, Win32)\r\nCopyright (c) StarWind Software 2003-2009. All rights reserved.\r\n\r\n\r\n",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.5067667961120605,
"total": 11.22574782371521
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:54:00.758311+00:00",
"host": "technotron.asuscomm.com",
"ip": "95.165.2.26",
"port": 3261
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug technotron.asuscomm.com 3261
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=technotron.asuscomm.com port=3261
ERROR client.py:1318 technotron.asuscomm.com:3261: TCP connection to technotron.asuscomm.com:3261 timed out after 30.0s