50.116.29.47 (echochamber.zapto.org)
echochamber.zapto.org:3640
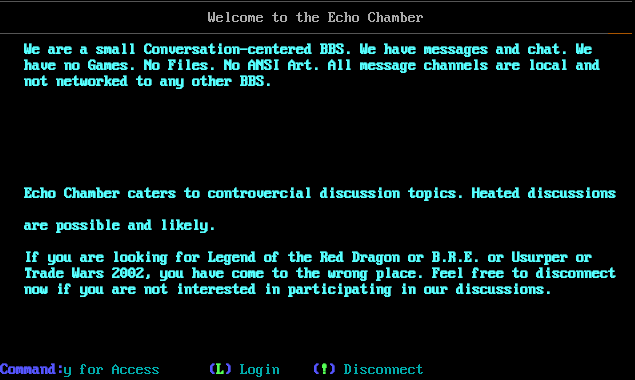
Connection Banner:
Server URLs
- Telnet: echochamber.zapto.org:3640
Server Location: 🇺🇸 United States (GeoIP)
Listing
BBS Name: Echo Chamber BBS (from listing)
Sysop: madman
Listed Location: Sacramento, CA, USA
BBS Software
Detected: Mystic BBS
Encoding
Effective encoding: cp437
Override: cp437 (from bbslist.txt)
Scanner detected: cp437
Telnet Fingerprint
This fingerprint is shared by 186 other servers.
Options offered by server: ECHO, SGA
Options requested from client: BINARY, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "aac0d9e4a94e81dc",
"fingerprint-data": {
"offered-options": [
"ECHO",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"BINARY",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\u001b[0m\n\u001b[1;34m\u001b[24;1H\u001b[0m\u001b[1;1H\u001b[1;1H\u001b[2J\u001b[1;1H\u001b[1m\u001b[0;1;30m\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\n\u001b[3;1H\u001b[3;27H\u001b[0mWelcome to the Echo Chamber\n\u001b[5;1H\u001b[1m\u001b[0;1;30m\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u001b[0m\u001b[33m\u2500\u2500\u2500\n\u001b[7;1H\u001b[7;4H\u001b[0;1;33m\u001b[0;1;36mWe are a small Conversation-centered BBS. We have messages and chat. We\n\u001b[9;1H\u001b[9;4Hhave no Games. No Files. No ANSI Art. All message channels are local and\n\u001b[11;1H\u001b[11;4Hnot networked to any other BBS. \n\u001b[12;1H\n\u001b[13;1H\u001b[13;4HEcho Chamber caters to controvercial discussion topics. Heated discussions\n\u001b[15;1H\u001b[15;4Hare possible and likely. \n\u001b[16;1H\n\u001b[17;1H\u001b[17;4HIf you are looking for Legend of the Red Dragon or B.R.E. or Usurper or\n\u001b[19;1H\u001b[19;4HTrade Wars 2002, you have come to the wrong place. Feel free to disconnect\n\u001b[21;1H\u001b[21;4Hnow if you are not interested in participating in our discussions.\r\n\u001b[23;1H\r\n\u001b[24;1H\u001b[0;1;33mMatrix Login Menu\r\u001b[0m\n\u001b[1;33m\u001b[24;1H\r\u001b[0m\n\u001b[1;33m\u001b[24;1H\u001b[0;1;34m(\u001b[0;1;32mA\u001b[0;1;34m) \u001b[0m\u001b[36mApply for Access\u001b[24;27H\u001b[0;1;36m\u001b[0;1;34m(\u001b[0;1;32mL\u001b[0;1;34m) \u001b[0m\u001b[36mLogin\u001b[24;40H\u001b[0;1;36m\u001b[0;1;34m(\u001b[0;1;32m!\u001b[0;1;34m) \u001b[0m\u001b[36mDisconnect\u001b[24;40H\r\u001b[0m\n\u001b[36m\u001b[24;1H\r\u001b[0m\n\u001b[36m\u001b[24;1H\u001b[0;1;36m\u001b[0;1;34mCommand: ",
"banner_before_return": "\u001b[1;1H\u001b[2J\u001b[1;1H\u001b[?1000h\fMystic BBS Version 1.12 A49\r\nCopyright (C) 1997-2024 By James Coyle\r\n\r\nDetecting terminal emulation: \u001b[s\u001b[255B\u001b[255C\u001b[6n\u001b[uANSI detected.\r\n\u001b[6;1H\u001b[1;1H\u001b[1;1H\u001b[2J\u001b[1;1H\u001b[1m\u001b[0;1;30m\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\n\u001b[3;1H\u001b[3;27H\u001b[0mWelcome to the Echo Chamber\n\u001b[5;1H\u001b[1m\u001b[0;1;30m\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u001b[0m\u001b[33m\u2500\u2500\u2500\n\u001b[7;1H\u001b[7;4H\u001b[0;1;33m\u001b[0;1;36mWe are a small Conversation-centered BBS. We have messages and chat. We\n\u001b[9;1H\u001b[9;4Hhave no Games. No Files. No ANSI Art. All message channels are local and\n\u001b[11;1H\u001b[11;4Hnot networked to any other BBS. \n\u001b[12;1H\n\u001b[13;1H\u001b[13;4HEcho Chamber caters to controvercial discussion topics. Heated discussions\n\u001b[15;1H\u001b[15;4Hare possible and likely. \n\u001b[16;1H\n\u001b[17;1H\u001b[17;4HIf you are looking for Legend of the Red Dragon or B.R.E. or Usurper or\n\u001b[19;1H\u001b[19;4HTrade Wars 2002, you have come to the wrong place. Feel free to disconnect\n\u001b[21;1H\u001b[21;4Hnow if you are not interested in participating in our discussions.\r\n\u001b[23;1H\r\n\u001b[24;1H\u001b[0;1;33mMatrix Login Menu\r\u001b[0m\n\u001b[1;33m\u001b[24;1H\r\u001b[0m\n\u001b[1;33m\u001b[24;1H\u001b[0;1;34m(\u001b[0;1;32mA\u001b[0;1;34m) \u001b[0m\u001b[36mApply for Access\u001b[24;27H\u001b[0;1;36m\u001b[0;1;34m(\u001b[0;1;32mL\u001b[0;1;34m) \u001b[0m\u001b[36mLogin\u001b[24;40H\u001b[0;1;36m\u001b[0;1;34m(\u001b[0;1;32m!\u001b[0;1;34m) \u001b[0m\u001b[36mDisconnect\u001b[24;40H\r\u001b[0m\n\u001b[36m\u001b[24;1H\r\u001b[0m\n\u001b[36m\u001b[24;1H\u001b[0;1;36m\u001b[0;1;34mCommand: ",
"dsr_replies": 1,
"dsr_requests": 1,
"encoding": "cp437",
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"ECHO": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"SGA": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"BINARY": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"SNDLOC": false,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5046689510345459,
"total": 11.105602264404297
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:23:50.472609+00:00",
"host": "echochamber.zapto.org",
"ip": "50.116.29.47",
"port": 3640
},
{
"connected": "2026-04-05T19:15:11.201282+00:00",
"host": "echochamber.zapto.org",
"ip": "50.116.29.47",
"port": 3640
},
{
"connected": "2026-04-07T05:59:58.817189+00:00",
"host": "echochamber.zapto.org",
"ip": "50.116.29.47",
"port": 3640
},
{
"connected": "2026-04-08T16:57:25.720432+00:00",
"host": "echochamber.zapto.org",
"ip": "50.116.29.47",
"port": 3640
},
{
"connected": "2026-04-10T00:29:34.653070+00:00",
"host": "echochamber.zapto.org",
"ip": "50.116.29.47",
"port": 3640
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug echochamber.zapto.org 3640
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=echochamber.zapto.org port=3640
INFO client_base.py:188 Connected to <Peer 50.116.29.47 3640>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC DO SNDLOC
DEBUG stream_writer.py:1887 handle_do(SNDLOC)
DEBUG stream_writer.py:1995 DO SNDLOC not supported.
DEBUG stream_writer.py:3384 local_option[SNDLOC] = False
DEBUG stream_writer.py:1024 send IAC WONT SNDLOC
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:789 WILL ECHO unsolicited
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:789 WILL SGA unsolicited
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO BINARY
DEBUG stream_writer.py:1887 handle_do(BINARY)
DEBUG stream_writer.py:3384 pending_option[WILL + BINARY] = True
DEBUG stream_writer.py:1024 send IAC WILL BINARY
DEBUG stream_writer.py:3384 local_option[BINARY] = True
DEBUG stream_writer.py:3384 pending_option[WILL + BINARY] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSSP
DEBUG stream_writer.py:2199 handle_wont(MSSP)
DEBUG stream_writer.py:3384 remote_option[MSSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG client_base.py:510 negotiation complete after 0.17s.
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT CHARSET
DEBUG stream_writer.py:2199 handle_wont(CHARSET)
DEBUG stream_writer.py:3384 remote_option[CHARSET] = False
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:844 connection for server fingerprint aac0d9e4a94e81dc
INFO client_base.py:120 Connection closed to <Peer 50.116.29.47 3640>
madmanbbs.ddns.net:23
Connection Banner:
![Mystic BBS Version 1.12 A49 Copyright (C) 1997-2024 By James Coyle Detecting terminal emulation: +-------------------- -- - : botcheck v1.2 >> Phenom Productions : Connected to: Madman with a Blue Box (nODE_2) : Running: Mystic BBS v1.12 A49 (Linux) +----------- -- - Press [.ESC.] twice within 15 seconds to CONTINUE... Welcome to: ۰ ۰ ۰ ۰ ۱ ۱ ۱ ۱ ۱ ۲ Name : ۲۲ ۲۲ Password : ܲ۲ ۲ Ŀ Ŀ "I don't know you, and I never forget a face." Your name cannot be found. Maybe you're wearing a disguise? If you've mistyped your name, answer NO below and you will be able to enter again. Otherwise, answer YES to become a Companion. Madman [Query] Do you wish to be one of The Doctor's Companions? YES Y NO N NO N YES Y NO N NO N](../_images/banner_a905ed6a0bcd.png)
Server URLs
- Telnet: madmanbbs.ddns.net:23
Server Location: 🇺🇸 United States (GeoIP)
BBS Software
Detected: Mystic BBS
Encoding
Effective encoding: utf-8
Override: utf-8 (from bbslist.txt)
Scanner detected: utf-8
Telnet Fingerprint
This fingerprint is shared by 186 other servers.
Options offered by server: ECHO, SGA
Options requested from client: BINARY, TTYPE
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "aac0d9e4a94e81dc",
"fingerprint-data": {
"offered-options": [
"ECHO",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"BINARY",
"TTYPE"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[0;1m\r\n\u001b[20;1H\u001b[1;1H\u001b[2J\u001b[1;1H\r\n\u001b[2;1H\u001b[0m\u001b[1m \u001b[0;1;31m\udcda\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\u013f \u001b[0m\u001b[35m\udcda\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\u013f\r\n\u001b[4;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3\u001b[4;11H\u001b[0m\u001b[33m\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\u001b[4;26H\u001b[0;1;33m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3\u001b[4;40H\udcb3\r\n\u001b[6;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[33m\udcdc\udcdf\udcdf \udcdc\udcdc\u001b[6;19H\udcdf\udcdf\udcdc \u001b[0;1;33m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3 \"\u001b[0;1;35m\u001b[0;1;36mI don't know you, and I never forget a face.\" \u001b[0m\u001b[35m\udcb3\r\n\u001b[8;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[33m\udcdc\udcdf \udcdf \u001b[0;1;33m\u001b[0;1;30m\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc \u001b[0m\u001b[33m\udcdb \u001b[0;1;33m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3\u001b[8;40H\udcb3\r\n\u001b[10;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[33m\udcdb \udcdb \u001b[0;1;33m\u001b[0;1;30m\udcdb\u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;30m\u001b[0;1;30;43m\udcdb\u001b[10;22H\u001b[0m\u001b[33m\udcdb \u001b[0;1;33m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3 \u001b[0;1;35m\u001b[0;1;33mYour name cannot be found.\u001b[11;38H\u001b[0m\u001b[35m\udcb3\r\n\u001b[12;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[33m\udcdb \udcdf\u001b[0;1;33m\u001b[0;1;30m\udcdc\u001b[0;1m\u001b[0;1;43m\udcdc\u001b[0m\u001b[33m\udcdf\udcdf\u001b[0m\udcdb\udcdb\u001b[1m\u001b[0;1;43m\udcdc\u001b[0m\u001b[30m\u001b[0;30;43m\udcdc\udcdc\u001b[0;43m\udcdb\u001b[1m\u001b[0;1;30;43m\u001b[0;1;30m\udcdb \u001b[0m\u001b[33m\udcdb \u001b[0;1;33m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3\u001b[12;40H\udcb3\r\n\u001b[14;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[33m\udcdf\udcdc \u001b[0;1;33m\u001b[0;1;30m\u001b[0;1;30;43m\udcdb\u001b[0;1;43m\u001b[0;1;47m\udcdf\u001b[0m\udcdc \udcdb\udcdb\u001b[1m\u001b[0;1;47m\udcdf\u001b[0m\udcdc\udcdc\udcdb\u001b[1m\u001b[0;1;30m\udcdb \udcdc\u001b[0m\u001b[33m\udcdf \u001b[0;1;33m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3 \u001b[0;1;35m\u001b[0;1;33mMaybe you're wearing a disguise?\u001b[15;38H\u001b[0m\u001b[35m\udcb3\r\n\u001b[16;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3\u001b[16;11H\u001b[0;1;30m\u001b[0;1;30;47m\udcdb\u001b[0m\u001b[0;47m\udcdb\u001b[0m\udcdc\udcdc\udcdc\udcdb\udcdf\udcdb\udcdb\u001b[1m\u001b[0;1;30m\udcdb \udcdf \u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3\u001b[16;40H\udcb3\r\n\u001b[18;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3\u001b[18;11H\u001b[0;1;30m\udcdf\u001b[0;1;30;47m\udcdc \u001b[0m\u001b[30m\u001b[0;30;47m\udcdf\udcdf\udcdf\u001b[0;47m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;30m\udcdb \u001b[0m\u001b[33m\udcdb \u001b[0;1;33m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3 \u001b[0;1;35m\u001b[0;1;33mIf you've mistyped your name, answer NO below \u001b[0m\u001b[35m\udcb3\r\n\u001b[20;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3\u001b[20;12H\u001b[0;1;30m\udcdf\u001b[0;1;30;47m\udcdc\udcdc\udcdc\udcdc\udcdc\u001b[0;1;30m\udcdf \u001b[0m\u001b[33m\udcdf\u001b[20;26H\u001b[0;1;33m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3 \u001b[0;1;35m\u001b[0;1;33mand you will be able to enter again.\u001b[21;38H\u001b[0m\u001b[35m\udcb3\r\n\u001b[22;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[33m\udcdc \u001b[0;1;33m\u001b[0;1m\udcdb\udcdc\udcdc\u001b[0m\u001b[30m\u001b[0;30;41m\udcdf\udcdf\u001b[0;1;30;41m\u001b[0;1;41m\u001b[0;1m\udcdc\udcdc\udcdb \u001b[0m\u001b[33m\udcdb\udcdc\udcdc \u001b[0;1;33m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3\u001b[22;40H\udcb3\r\n\u001b[24;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[33m\udcdb\udcdb\udcdc\u001b[0;1;33m\u001b[0;1m\udcdf\u001b[0m\u001b[31m\u001b[0;31;41m\udcdb\udcdb\u001b[0;1;31;41m\u001b[0;1;41m\udcdf\udcdf\u001b[0m\u001b[31m\u001b[0;31;41m\udcdb\udcdb\u001b[0;1;31;41m\u001b[0;1;41m\u001b[0;1m\udcdf \u001b[0m\u001b[33m\udcdb\udcdb\udcdb\udcdb \u001b[0;1;33m\u001b[0;1;31m\udcb3 \u001b[0m\u001b[35m\udcb3 \u001b[0;1;35m\u001b[0;1;33mOtherwise, answer YES to become a Companion. \u001b[0m\u001b[35m\udcb3\r\u001b[0m\n\u001b[35m\u001b[24;1H \u001b[0;1;35m\u001b[0;1;31m\udcb3\u001b[24;26H\udcb3 \u001b[0m\u001b[35m\udcb3\u001b[24;40H\udcb3\r\u001b[0m\n\u001b[35m\u001b[24;1H \u001b[0;35;44m \u001b[0;1;35;44m\u001b[0;1;36;44mMadman \u001b[24;28H\u001b[0m\u001b[35m\udcc0\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcd9\r\u001b[0m\n\u001b[35m\u001b[24;1H\u001b[0m\r\n\u001b[24;1H\u001b[17;40H\u001b[1;34m\udcda\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\u001b[17;40H\udcbf\u001b[17;40H\u001b[0;1;36;44m[Query]\u001b[18;40H\u001b[0;1;34m\udcb3 \u001b[18;40H\u001b[0;34m\u001b[0m\u001b[34m\udcb3\u001b[19;40H\u001b[0;1;34m\udcb3 \u001b[19;40H\u001b[0;34m\u001b[0m\u001b[34m\udcb3\u001b[20;40H\u001b[0;1;34m\udcb3 \u001b[20;40H\u001b[0;34m\u001b[0m\u001b[34m\udcb3\u001b[21;40H\u001b[0;1;34m\udcb3 \u001b[21;40H\u001b[0;34m\u001b[0m\u001b[34m\udcb3\u001b[22;40H\u001b[0;1;34m\udcc0\u001b[22;40H\u001b[0;34m\u001b[0m\u001b[34m\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcc4\udcd9\u001b[19;40H\u001b[0mDo you wish to be one of The Doctor's Companions?\u001b[21;40H YES \u001b[21;40H\u001b[1mY\u001b[21;40H\u001b[0m NO \u001b[21;40H\u001b[1mN\u001b[21;40H\u001b[0;1;44m NO \u001b[21;40HN\u001b[21;40H\u001b[0m YES \u001b[21;40H\u001b[1mY\u001b[21;40H\u001b[0m NO \u001b[21;40H\u001b[1mN\u001b[21;40H\u001b[0;1;44m NO \u001b[21;40HN",
"banner_before_return": "\u001b[1;1H\u001b[2J\u001b[1;1H\u001b[?1000h\fMystic BBS Version 1.12 A49\r\nCopyright (C) 1997-2024 By James Coyle\r\n\r\nDetecting terminal emulation: \u001b[s\u001b[255B\u001b[255C\u001b[6n\u001b[u\u001b[1;1H\u001b[1;1H\u001b[2J\u001b[1;1H\u001b[36m+-------------------- -- -\r\n\u001b[2;1H: \u001b[0;36;46m\u001b[0;1;36;46m\u001b[0;1;46m botcheck v1.2 \u001b[0;1m \u001b[0;1;32m>\u001b[0m\u001b[36m> \u001b[0;1;36mPhenom Productions\r\n\u001b[3;1H\u001b[0m\u001b[36m: \u001b[0mConnected to: \u001b[1mMadman with a Blue Box \u001b[0m(\u001b[36mnODE_\u001b[0;1;36m2\u001b[0m)\r\n\u001b[5;1H\u001b[36m: \u001b[0mRunning: \u001b[1mMystic BBS v1.12 A49 \u001b[0m(\u001b[1m\u001b[0;1;36mLinux\u001b[0m)\r\n\u001b[6;1H\u001b[36m+----------- -- -\r\n\u001b[7;1H\r\n\u001b[8;1H\u001b[0mPress [\u001b[1m\u001b[0;1;30m.\u001b[0;1mESC\u001b[0;1;30m.\u001b[0m] \u001b[1m\u001b[0;1;32mtwice \u001b[0mwithin \u001b[1m15\u001b[0m seconds to \u001b[1mCONTINUE\u001b[0;1;33m...\u001b[9;1H\r\n\u001b[10;1H\u001b[?33l\u001b[?35l\u001b[0;0 D\u001b[1;1H\u001b[2J\u001b[1;1H\u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb \u001b[1m\u001b[0;1;34m\u001b[0;1;34;46m\udcb0\udcb0\udcb0\udcb0\u001b[3;23H\u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\u001b[0;41m \u001b[1m\u001b[0;1;32;41mWelcome to: \u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf \udcdf\udcdf\udcdf\udcdf \udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdb\udcdb\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\u001b[0m\udcdb\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc \u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdf\udcdf \u001b[34m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb \u001b[0m\udcdf\udcdf\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0;1;34;47m \u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0m\udcdb\udcdb\udcdb\udcdb \u001b[34m\udcdb\udcdb\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdb\udcdb \u001b[0m\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0;1;34;47m \u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0;1;34;47m\udcdc\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0;1;34;47m\udcdc\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0m\udcdb\udcdb\udcdb\udcdb \u001b[34m\udcdb\udcdb \u001b[0;1;34m\u001b[0;1;36m\udcdb\udcdb \udcdb\udcdf\udcdb \udcdb \udcdb \udcdb\udcdf \udcdf \udcdb\udcdf\udcdc \udcdb\udcdf\udcdb \udcdf\udcdc\udcdf \u001b[0m\u001b[34m\udcdb\udcdb \u001b[0m\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;44m\udcdf\u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0;1;34;44m\udcdf\u001b[0m\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;44m\udcdf\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;44m\udcdf\u001b[0m\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;44m\udcdf\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0m\udcdb\udcdb\udcdb\udcdb \u001b[34m\udcdb\udcdb \u001b[0;1;34m\u001b[0;1;36m\udcdf \udcdf\udcdf\udcdf \udcdf\udcdf \udcdf \udcdf\udcdf \udcdf \udcdf\udcdf\udcdf \udcdf\udcdf\udcdf \udcdf \udcdf \u001b[0m\u001b[34m\udcdb\udcdb \u001b[0m\udcdb\udcdb\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf \udcdf \udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\udcdf \u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf \u001b[0;47m\u001b[0m\udcdb\udcdb\udcdb\udcdb \u001b[34m\udcdf\udcdf\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdf\udcdf \u001b[0m\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\u001b[0m\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc \u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcb0\udcdb\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdb\udcdb \udcdb\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\u06f0\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcb0\udcdb \u001b[0;1;34m\u001b[0;1;36m\udcdd\u001b[0;1;36;44m\udcdc\udcdc \udcdc\udcdc\udcdc\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;44m\udcdc\udcdc\u001b[0;1;36m\udcdd\u001b[0;1;34m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\udcdb\udcdb \udcdb \u001b[0;1;34m\u001b[0;1;36m\udcdd\u001b[0;1;36;44m\udcdc\udcdc \udcdc\udcdc\udcdc\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;44m\udcdc\udcdc\u001b[0;1;36m\udcdd\u001b[0;1;34m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\u06f0\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0;1;34;47m\udcdc\u001b[0;1;34m\udcdb\u001b[0m\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0;1;34;47m\udcdc\u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcb0\udcdb \u001b[0;1;34m\u001b[0;1;36m\udcdd\u001b[0;1;36;46m\udcb0\udcb0\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;46m\udcb0\udcb0\udcb0\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;46m\udcb0\udcb0\u001b[0;1;36m\udcdd\u001b[0;1;34m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\udcdb\udcdb \udcdb \u001b[0;1;34m\u001b[0;1;36m\udcdd\u001b[0;1;36;46m\udcb0\udcb0\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;46m\udcb0\udcb0\udcb0\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;46m\udcb0\udcb0\u001b[0;1;36m\udcdd\u001b[0;1;34m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\u06f0\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;44m\udcdf\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;44m\udcdf\u001b[0;1;34m\udcdb\u001b[0m\udcdb\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;44m\udcde\u001b[0;1;34m\udcdb\u001b[0m\udcdb\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\udcdb\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcb1\udcdb \u001b[0;1;34m\u001b[0;1;36m\udcdd\u001b[0;1;36;44m\udcdc\udcdc\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;44m\udcdc\udcdc\udcdc\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;44m\udcdc\udcdc\u001b[0;1;36m\udcdd\u001b[0;1;34m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\udcdb\udcdb \udcdb \u001b[0;1;34m\u001b[0;1;36m\udcdd\u001b[0;1;36;44m\udcdc\udcdc\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;44m\udcdc\udcdc\udcdc\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;44m\udcdc\udcdc\u001b[0;1;36m\udcdd\u001b[0;1;34m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\u06f0\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\u001b[0;47m\u001b[0m\udcdb\udcdb\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf \u001b[0;47m\u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcb1\udcdb \u001b[0;1;34m\u001b[0;1;36m\udcdd\u001b[0;1;36;46m\udcb0\udcb0\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;46m\udcb0\udcb0\udcb0\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;46m\udcb0\udcb0\u001b[0;1;36m\udcdd\u001b[0;1;34m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\udcdb\udcdb \udcdb \u001b[0;1;34m\u001b[0;1;36m\udcdd\u001b[0;1;36;46m\udcb0\udcb0\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;46m\udcb0\udcb0\udcb0\u001b[0m\u001b[34m\udcdb\u001b[0;1;34m\u001b[0;1;36m\u001b[0;1;36;46m\udcb0\udcb0\u001b[0;1;36m\udcdd\u001b[0;1;34m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\u06f1\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\u001b[0m\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc\u001b[0m\udcdb\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\udcdc\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdc\u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcb1\udcdb \u001b[0;1;34m\u001b[0;1;34;44m\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdb\u001b[0m\u001b[34m\udcdb\udcdb \udcdb \u001b[0;1;34m\u001b[0;1;34;44m\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdb\u001b[0m\u001b[34m\u06f1\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdf\u001b[0m\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0;1;34;47m \u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcb2\udcdb\udcdb\u001b[0;34;44m \u001b[0;34m\udcdb\udcdb \udcdb\udcdb\u001b[0;34;44m \u001b[0;34m\u06f1\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0;1;34;47m\udcdc\udcdf\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0;1;34;47m\udcdc\u001b[0m\udcdb\udcdb\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0;1;34;47m\udcdc\udcdf\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\u001b[0;1;34;47m\udcdf\u001b[0;1;34m\udcdb\u001b[0;1;34;47m\udcdc\udcdf\u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcb2\udcdb\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdb\udcdb \udcdb\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\u06f1\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\udcdb\u001b[0;1;34;47m\udcdc\udcdc\u001b[0m\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;34;44m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\u001b[1m\u001b[0;1;34m\udcdb\u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcb2\udcdb \u001b[0;30m\u001b[0;30;46m\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\u001b[0;1;30;46m\u001b[0;1;34;46m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\udcdb\udcdb \udcdb \udcb0\udcb0\udcb0\udcb1\udcb1\udcb1\udcb2\udcb2\udcb2\udcdb\udcdb\u001b[0;1;34m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\u06f1\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[0;47m \u001b[34m\udcdf\udcdf\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\udcdf\u001b[0;47m\u001b[0m\udcdb\u001b[34m\u001b[0;34;47m\udcdf\u001b[0;47m\u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcdb\udcdb \u001b[0;30m\u001b[0;30;46m\udcb0\u001b[0;1;30;46m\u001b[0;1;36;46m\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\u001b[0m\u001b[30m\u001b[0;30;46m\udcb0\u001b[0;1;30;46m\u001b[0;1;34;46m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\udcdb\udcdb \udcdb \udcb0\udcb0\udcb1\udcb1\udcb1\udcb2\udcb2\udcb2\udcdb\udcdb\u001b[0;1;34m\u001b[0;1;34;44m\udcb1\udcdb\u001b[0m\u001b[34m\u06f2\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;32;44mName : \u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcdb\udcdb \u001b[0;30m\u001b[0;30;46m\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\udcb0\u001b[0;1;30;46m\u001b[0;1;34;46m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\udcdb\udcdb \udcdb \udcb0\udcb1\udcb1\udcb1\udcb2\udcb2\udcb2\udcdb\u06f2\u001b[0;1;34m\u001b[0;1;34;44m\udcb1\udcdb\u001b[0m\u001b[34m\u06f2\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcdb\udcdb \u001b[0;30m\u001b[0;30;46m\udcb0\u001b[0;1;30;46m\u001b[0;1;36;46m\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\u001b[0m\u001b[30m\u001b[0;30;46m\udcb0\u001b[0;1;30;46m\u001b[0;1;34;46m\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\udcdb\udcdb \udcdb \udcb1\udcb1\udcb1\udcb2\udcb2\udcb2\udcdb\u06f2\udcb2\u001b[0;1;34m\u001b[0;1;34;44m\udcb2\udcdb\u001b[0m\u001b[34m\u06f2\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\u001b[0;44m \u001b[1m\u001b[0;1;32;44mPassword : \u001b[0m\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcdb\udcdb \u001b[0;1;34m\u001b[0;1;34;46m\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\u001b[0;1;34;44m\udcdb\u001b[0m\u001b[34m\udcdb\udcdb \udcdb \u001b[0;1;34m\u001b[0;1;34;44m\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\udcdc\u0732\udcdb\u001b[0m\u001b[34m\u06f2\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcdb\udcdb\udcdb\u001b[0;34;44m \u001b[0;34m\udcdb\udcdb \udcdb\udcdb\u001b[0;34;44m \u001b[0;34m\u06f2\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdd\u001b[34m\udcdb\udcdb\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdb\udcdb \udcdb\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdf\udcdb\udcdb\u001b[0m\udcde\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\udcdb\r\n\u001b[24;1H\u001b[24;40H\u001b[18;40H\u001b[1;34;44m \u001b[0;1;44m\u001b[19;40H",
"dsr_replies": 1,
"dsr_requests": 1,
"encoding": "utf-8",
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"ECHO": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"SGA": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"BINARY": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"SNDLOC": false,
"TTYPE": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5084142684936523,
"total": 11.16000485420227
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:05:26.184587+00:00",
"host": "madmanbbs.ddns.net",
"ip": "50.116.29.47",
"port": 23
},
{
"connected": "2026-04-05T19:02:12.805777+00:00",
"host": "madmanbbs.ddns.net",
"ip": "50.116.29.47",
"port": 23
},
{
"connected": "2026-04-07T06:13:50.841665+00:00",
"host": "madmanbbs.ddns.net",
"ip": "50.116.29.47",
"port": 23
},
{
"connected": "2026-04-10T00:33:19.865793+00:00",
"host": "madmanbbs.ddns.net",
"ip": "50.116.29.47",
"port": 23
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug madmanbbs.ddns.net 23
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=madmanbbs.ddns.net port=23
INFO client_base.py:188 Connected to <Peer 50.116.29.47 23>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC DO SNDLOC
DEBUG stream_writer.py:1887 handle_do(SNDLOC)
DEBUG stream_writer.py:1995 DO SNDLOC not supported.
DEBUG stream_writer.py:3384 local_option[SNDLOC] = False
DEBUG stream_writer.py:1024 send IAC WONT SNDLOC
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:789 WILL ECHO unsolicited
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:789 WILL SGA unsolicited
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO BINARY
DEBUG stream_writer.py:1887 handle_do(BINARY)
DEBUG stream_writer.py:3384 pending_option[WILL + BINARY] = True
DEBUG stream_writer.py:1024 send IAC WILL BINARY
DEBUG stream_writer.py:3384 local_option[BINARY] = True
DEBUG stream_writer.py:3384 pending_option[WILL + BINARY] = False
DEBUG stream_writer.py:773 recv IAC DO TTYPE
DEBUG stream_writer.py:1887 handle_do(TTYPE)
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = True
DEBUG stream_writer.py:1024 send IAC WILL TTYPE
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = True
DEBUG stream_writer.py:3384 local_option[TTYPE] = True
DEBUG stream_writer.py:3384 pending_option[WILL + TTYPE] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSSP
DEBUG stream_writer.py:2199 handle_wont(MSSP)
DEBUG stream_writer.py:3384 remote_option[MSSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:767 begin sub-negotiation SB TTYPE
DEBUG stream_writer.py:754 sub-negotiation cmd TTYPE SE completion byte
DEBUG stream_writer.py:3384 pending_option[SB + TTYPE] = False
DEBUG stream_writer.py:2404 recv TTYPE SEND: b''
DEBUG stream_writer.py:2416 send IAC SB TTYPE IS b'xterm-256color' IAC SE
DEBUG client_base.py:510 negotiation complete after 0.15s.
DEBUG client_base.py:268 SyncTERM font switch: cp437
DEBUG client_base.py:270 ignoring font switch, explicit encoding: utf-8
DEBUG server_fingerprinting.py:1082 SyncTERM font switch detected: cp437
DEBUG server_fingerprinting.py:1084 ignoring font switch, explicit encoding: utf-8
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT CHARSET
DEBUG stream_writer.py:2199 handle_wont(CHARSET)
DEBUG stream_writer.py:3384 remote_option[CHARSET] = False
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:844 connection for server fingerprint aac0d9e4a94e81dc
INFO client_base.py:120 Connection closed to <Peer 50.116.29.47 23>