192.95.118.156 (amigaunderground.com)
amigaunderground.com:1985
Connection Banner:
![\*\*\* geoip Mancelona, United States done. \*\*\* ip threat detection LOW done. Welcome to _____ __________ .___ _____ / _ \\ \\______ \\ \| \| / _ \\ / /_\\ \\ \| _/ \| \| / /_\\ \\ / \| \\ \| \| \\ \| \| / \| \\ \\____\|____/ \|____\|___/ \|___\| \\____\|____/ Resonance Engine v1.0 This private signal grid is a privilege, not a promise. By syncing in, you consent to full-spectrum monitoring: every pulse, keystroke, and data fragment is logged, traced, and guarded. We welcome the curious, the sharp, the free thinkers. We burn zero tolerance for harassment, abuse, spam, or signal-jamming noise. Be clean. Be clever. Keep the neon flowing. Disrupt the harmony and your carrier wave ends permanently. Lock in. Transmit wisely. Welcome to the resonance. User names and passwords are 'case sensitive'. Welcome to _____ __________ .___ _____ / _ \\ \\______ \\ \| \| / _ \\ / /_\\ \\ \| _/ \| \| / /_\\ \\ / \| \\ \| \| \\ \| \| / \| \\ \\____\|____/ \|____\|___/ \|___\| \\____\|____/ Resonance Engine v1.0 This private signal grid is a privilege, not a promise. By syncing in, you consent to full-spectrum monitoring: every pulse, keystroke, and data fragment is logged, traced, and guarded. We welcome the curious, the sharp, the free thinkers. We burn zero tolerance for harassment, abuse, spam, or signal-jamming noise. Be clean. Be clever. Keep the neon flowing. Disrupt the harmony and your carrier wave ends permanently. Lock in. Transmit wisely. Welcome to the resonance. User names and passwords are 'case sensitive'. Username or NEW: ]EFf[Z]EFf[Z User not found.](../_images/banner_d58d2e91da17.png)
Server URLs
- Telnet: amigaunderground.com:1985
- Website: http://amigaunderground.com
Server Location: 🇺🇸 United States (GeoIP)
Listing
BBS Name: Amiga Underground (from listing)
Sysop: karynroberts
Listed Location: Edgewood, NM, USA
BBS Software
Reported: AmiExpress
Encoding
Effective encoding: topaz
Override: topaz (from bbslist.txt)
Scanner detected: ascii
Telnet Fingerprint
This fingerprint is shared by 6 other servers.
Options requested from client: SGA
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "d4f3adfd6a3bbb9d",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [
"SGA"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\r\nUser not found.\r\r\n",
"banner_before_return": "\u001b[2J\u001b[H*** geoip Mancelona, United States done.\r\n*** ip threat detection LOW done.\r\n\u001b[2J\u001b[H Welcome to\r\n _____ __________ .___ _____\r\n / _ \\ \\______ \\ | | / _ \\\r\n / /_\\ \\ | _/ | | / /_\\ \\\r\n / | \\ | | \\ | | / | \\\r\n \\____|____/ |____|___/ |___| \\____|____/\r\n\r\n Resonance Engine v1.0\r\n\r\n This private signal grid is a privilege, not a promise. \r\n\r\n By syncing in, you consent to full-spectrum monitoring: every pulse,\r\n keystroke, and data fragment is logged, traced, and guarded.\r\n We welcome the curious, the sharp, the free thinkers.\r\n We burn zero tolerance for harassment, abuse, spam, or signal-jamming noise.\r\n Be clean. Be clever. Keep the neon flowing.\r\n Disrupt the harmony and your carrier wave ends \udce2\udc80\udc93 permanently.\r\n Lock in. Transmit wisely. Welcome to the resonance.\r\n\r\n User names and passwords are 'case sensitive'.\r\n\r\n\u001b[2J\u001b[H Welcome to\r\r\n _____ __________ .___ _____\r\r\n / _ \\ \\______ \\ | | / _ \\\r\r\n / /_\\ \\ | _/ | | / /_\\ \\\r\r\n / | \\ | | \\ | | / | \\\r\r\n \\____|____/ |____|___/ |___| \\____|____/\r\r\n\r\r\n Resonance Engine v1.0\r\r\n\r\r\n This private signal grid is a privilege, not a promise. \r\r\n\r\r\n By syncing in, you consent to full-spectrum monitoring: every pulse,\r\r\n keystroke, and data fragment is logged, traced, and guarded.\r\r\n We welcome the curious, the sharp, the free thinkers.\r\r\n We burn zero tolerance for harassment, abuse, spam, or signal-jamming noise.\r\r\n Be clean. Be clever. Keep the neon flowing.\r\r\n Disrupt the harmony and your carrier wave ends \udce2\udc80\udc93 permanently.\r\r\n Lock in. Transmit wisely. Welcome to the resonance.\r\r\n\r\r\n User names and passwords are 'case sensitive'.\r\r\n\r\r\n\u001b[1;36mUsername or NEW: \u001b[0m]EFf[Z]EFf[Z",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"ECHO": true,
"SGA": true
},
"server_requested": {
"SGA": true
}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 2.5844497680664062
}
}
},
"sessions": [
{
"connected": "2026-02-16T22:14:24.589787+00:00",
"host": "amigaunderground.com",
"ip": "192.95.118.156",
"port": 1985
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug amigaunderground.com 1985
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=amigaunderground.com port=1985
ERROR client.py:1296 amigaunderground.com:1985: [Errno 111] Connect call failed ('192.95.118.156', 1985)
amigaunderground.com:2002
Connection Banner:
Server URLs
- Telnet: amigaunderground.com:2002
Server Location: 🇺🇸 United States (GeoIP)
BBS Software
Reported: AmiExpress
Encoding
Effective encoding: topaz
Override: topaz (from bbslist.txt)
Scanner detected: ascii
Telnet Fingerprint
This fingerprint is shared by 142 other servers.
Options offered by server: BINARY, ECHO, SGA
Options requested from client: BINARY
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "e9e1390d6941c201",
"fingerprint-data": {
"offered-options": [
"BINARY",
"ECHO",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"CHARSET",
"COM_PORT",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"BINARY"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\n\r\r\nA login name is required.\r\n\r\nPlease enter your name (ENTER for none): ",
"banner_before_return": "\u0000Telnet connection detected.\n\r\n\rPlease enter your name (ENTER for none): ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"0x24": false,
"BINARY": true,
"ECHO": true,
"NEW_ENVIRON": false,
"SGA": true,
"STATUS": false
},
"server_requested": {
"0x24": false,
"0xf6": false,
"BINARY": true,
"LFLOW": false,
"LINEMODE": false,
"NAWS": false,
"NEW_ENVIRON": false,
"TSPEED": false,
"TTYPE": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.526007890701294,
"total": 11.31245231628418
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:21:22.927008+00:00",
"host": "amigaunderground.com",
"ip": "192.95.118.156",
"port": 2002
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug amigaunderground.com 2002
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=amigaunderground.com port=2002
ERROR client.py:1318 amigaunderground.com:2002: [Errno 111] Connect call failed ('192.95.118.156', 2002)
amigaunderground.com:2300
Connection Banner:
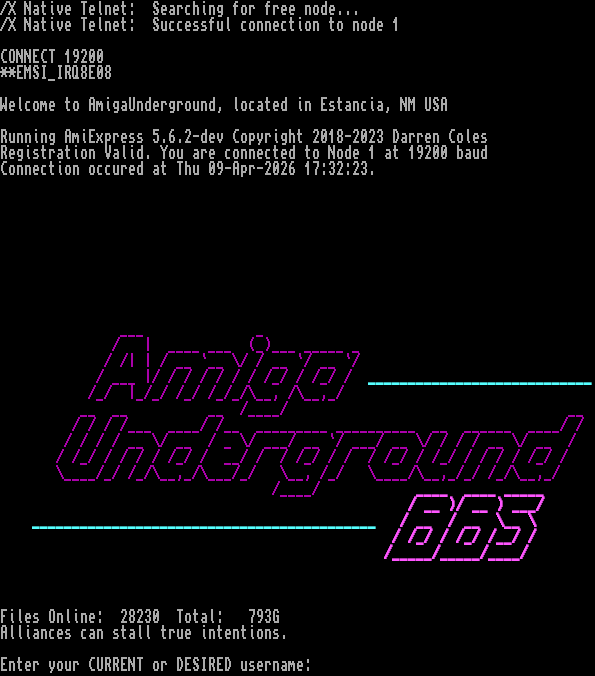
Server URLs
- Telnet: amigaunderground.com:2300
Server Location: 🇺🇸 United States (GeoIP)
BBS Software
Reported: AmiExpress
FidoNet
This server responded with an EMSI handshake sequence.
Encoding
Effective encoding: topaz
Override: topaz (from bbslist.txt)
Scanner detected: ascii
Telnet Fingerprint
This fingerprint is shared by 19 other servers.
Options offered by server: ECHO, SGA
Options requested from client: BINARY
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "cb06484bfba3244f",
"fingerprint-data": {
"offered-options": [
"ECHO",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"BINARY"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\n\r\nEnter your CURRENT or DESIRED username: ",
"banner_before_return": "\r\n/X Native Telnet: Searching for free node...\r\n/X Native Telnet: Successful connection to node 1\r\n\r\nCONNECT 19200\r\n**EMSI_IRQ8E08\r\n\r\n\u001b[0mWelcome to AmigaUnderground, located in Estancia, NM USA\r\n\r\nRunning AmiExpress 5.6.2-dev Copyright \udca92018-2023 Darren Coles\r\nRegistration Valid. You are connected to Node 1 at 19200 baud\r\nConnection occured at Thu 09-Apr-2026 17:32:23.\r\n\r\n\u001b[0m\u001b[0m\r\n\r\n\r\n\r\n\r\n\r\n\r\n\r\n \u001b[35m___ _\r\n\u001b[37m \u001b[35m/ | ____ ___ (_)___ _____ _\r\n\u001b[37m \u001b[35m/ /| | / __ `__ \\/ / __ `/ __ `/\r\n\u001b[37m \u001b[35m/ ___ |/ / / / / / / /_/ / /_/ / \u001b[1;36m____________________________\u001b[0m\r\n \u001b[35m/_/ |_/_/ /_/ /_/_/\\__, /\\__,_/\r\n\u001b[37m \u001b[35m__ __ __ /____/ __\u001b[37m\r\n \u001b[35m/ / / /___ ____/ /__ _________ __________ __ ______ ____/ /\u001b[37m\r\n \u001b[35m/ / / / __ \\/ __ / _ \\/ ___/ __ `/ ___/ __ \\/ / / / __ \\/ __ /\r\n\u001b[37m \u001b[35m/ /_/ / / / / /_/ / __/ / / /_/ / / / /_/ / /_/ / / / / /_/ /\r\n\u001b[37m \u001b[35m\\____/_/ /_/\\__,_/\\___/_/ \\__, /_/ \\____/\\__,_/_/ /_/\\__,_/\r\n\u001b[37m \u001b[35m/____/ \u001b[1m____ ____ _____\u001b[0;35m\r\n\u001b[37m \u001b[1;35m/ __ )/ __ ) ___/\u001b[0m\r\n \u001b[1;36m___________________________________________\u001b[0m \u001b[1;35m/ __ / __ \\__ \\\r\n\u001b[0m \u001b[1;35m/ /_/ / /_/ /__/ /\r\n\u001b[0m \u001b[1;35m/_____/_____/____/\r\n\u001b[0m\r\n\r\n\r\nFiles Online: 28230 Total: 793G\r\nAlliances can stall true intentions.\r\n\u001b[0m\u001b[0m\r\nEnter your CURRENT or DESIRED username: ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "ascii",
"option_states": {
"server_offered": {
"ECHO": true,
"SGA": true,
"STATUS": false
},
"server_requested": {
"BINARY": true,
"LINEMODE": false,
"NAWS": false,
"TSPEED": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5037479400634766,
"total": 11.090905666351318
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:07:22.204551+00:00",
"host": "amigaunderground.com",
"ip": "192.95.118.156",
"port": 2300
},
{
"connected": "2026-04-07T05:55:53.025854+00:00",
"host": "amigaunderground.com",
"ip": "192.95.118.156",
"port": 2300
},
{
"connected": "2026-04-10T00:31:38.632930+00:00",
"host": "amigaunderground.com",
"ip": "192.95.118.156",
"port": 2300
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug amigaunderground.com 2300
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=amigaunderground.com port=2300
INFO client_base.py:188 Connected to <Peer 192.95.118.156 2300>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC DO BINARY
DEBUG stream_writer.py:1887 handle_do(BINARY)
DEBUG stream_writer.py:3384 pending_option[WILL + BINARY] = True
DEBUG stream_writer.py:1024 send IAC WILL BINARY
DEBUG stream_writer.py:3384 local_option[BINARY] = True
DEBUG stream_writer.py:3384 pending_option[WILL + BINARY] = False
DEBUG stream_writer.py:773 recv IAC DONT NAWS
DEBUG stream_writer.py:2010 handle_dont(NAWS)
DEBUG stream_writer.py:3384 pending_option[WILL + NAWS] = False
DEBUG stream_writer.py:3384 local_option[NAWS] = False
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC DONT TSPEED
DEBUG stream_writer.py:2010 handle_dont(TSPEED)
DEBUG stream_writer.py:3384 pending_option[WILL + TSPEED] = False
DEBUG stream_writer.py:3384 local_option[TSPEED] = False
DEBUG stream_writer.py:773 recv IAC DONT LINEMODE
DEBUG stream_writer.py:2010 handle_dont(LINEMODE)
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = False
DEBUG stream_writer.py:3384 local_option[LINEMODE] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:789 WILL SGA unsolicited
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:789 WILL ECHO unsolicited
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG client_base.py:513 negotiation failed after 4.00s.
DEBUG client_base.py:519 failed-reply: 'WILL ZMP, WILL AARDWOLF, WILL MSDP, WILL GMCP, WILL MXP, WILL ATCP, WILL MSSP, WILL MSP,
WILL MCCP2_COMPRESS, WILL MCCP3_COMPRESS, DO ZMP, DO AARDWOLF, DO MSDP, DO GMCP, DO MXP, DO ATCP, DO MSSP, DO MSP, DO
MCCP2_COMPRESS, DO MCCP3_COMPRESS'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:844 connection for server fingerprint cb06484bfba3244f
INFO client_base.py:120 Connection closed to <Peer 192.95.118.156 2300>