ezycom.retroswim.net:2323
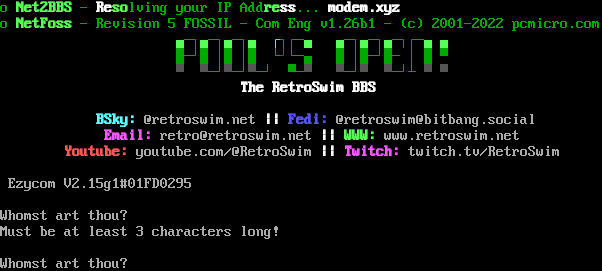
Connection Banner:
Server URLs
- Telnet: ezycom.retroswim.net:2323
Server Location: 🇦🇺 Australia (GeoIP)
Encoding
Effective encoding: cp437
Override: cp437 (from bbslist.txt)
Scanner detected: cp437
Telnet Fingerprint
This fingerprint is shared by 39 other servers.
Options offered by server: BINARY, ECHO, SGA
Options requested from client: BINARY, SGA
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "db901ebd131f6da3",
"fingerprint-data": {
"offered-options": [
"BINARY",
"ECHO",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"CHARSET",
"COM_PORT",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"BINARY",
"SGA"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\r\nMust be at least 3 characters long!\r\n\nWhomst art thou? ",
"banner_before_return": "|\u001b[2J\u001b[0;32mo \u001b[1mNet2BBS \u001b[0;32m- \u001b[1;37mRe\u001b[32mso\u001b[0;32mlving your IP Add\u001b[1mre\u001b[37mss\u001b[0;32m...\u001b[1;37m modem.xyz\n\r\r\u001b[0;32mo\u001b[1m NetFoss \u001b[0;32m- Revision 5 FOSSIL - Com Eng v1.26b1 - (c) 2001-2022 pcmicro.com\u001b[37m\r\n\u0000\u001b[22C\u001b[1;32m\u2584\u001b[0;32m\u2500\u2510\u001b[1m\u2584\u001b[0;32m\u2500\u2510\u001b[1m\u2584\u001b[0;32m\u2500\u2510\u001b[1m\u2584 \u250c\u001b[0;32m\u2510\u250c\u2500\u001b[1m\u2584 \u2584\u001b[0;32m\u2500\u2510\u001b[1m\u2584\u001b[0;32m\u2500\u2510\u001b[1m\u2584\u001b[0;32m\u2500\u2510\u250c\u2500\u001b[1m\u2584 \u2584\r\n\u001b[22C\u001b[0;32m\u2588\u2500\u2518\u2588 \u2502\u2588 \u2502\u2588 \u2514\u001b[1;30m\u2518\u001b[0;32m\u2514\u2500\u2584 \u2588 \u2502\u2588\u2500\u2518\u2588\u2500 \u2502 \u2588 \u2580\r\n\u001b[22C\u001b[1;30m\u2580 \u2580\u001b[0;32m\u2500\u2518\u001b[1;30m\u2580\u001b[0;32m\u2500\u2518\u001b[1;30m\u2580\u001b[0;32m\u2500\u2518 \u2580\u2500\u001b[1;30m\u2580 \u2580\u001b[0;32m\u2500\u2518\u001b[1;30m\u2580 \u2580\u001b[0;32m\u2500\u2518\u2534 \u001b[1;30m\u2580 \u2580\r\n\u001b[30C\u001b[37mThe RetroSwim BBS\r\n \r\n\u001b[12C\u001b[36mBSky: \u001b[0m@retroswim.net \u001b[1m|| \u001b[34mFedi: \u001b[0m@retroswim@bitbang.social\r\n\u001b[13C\u001b[1;35mEmail: \u001b[0mretro@retroswim.net \u001b[1m|| \u001b[32mWWW: \u001b[0mwww.retroswim.net\r\n\u001b[8C\u001b[1;31mYoutube: \u001b[0myoutube.com/@RetroSwim \u001b[1m|| \u001b[35mTwitch: \u001b[0mtwitch.tv/RetroSwim\r\n \r\n Ezycom V2.15g1#01FD0295\r\n\nWhomst art thou? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "cp437",
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"BINARY": true,
"ECHO": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"SGA": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"BINARY": true,
"ECHO": false,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"SGA": true,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.20184683799743652,
"total": 10.887760639190674
}
}
},
"sessions": [
{
"connected": "2026-04-05T18:54:26.148149+00:00",
"host": "ezycom.retroswim.net",
"ip": "103.95.113.91",
"port": 2323
},
{
"connected": "2026-04-07T06:32:11.437519+00:00",
"host": "ezycom.retroswim.net",
"ip": "103.95.113.91",
"port": 2323
},
{
"connected": "2026-04-08T17:03:19.051198+00:00",
"host": "ezycom.retroswim.net",
"ip": "103.95.113.91",
"port": 2323
},
{
"connected": "2026-04-10T00:34:31.933447+00:00",
"host": "ezycom.retroswim.net",
"ip": "103.95.113.91",
"port": 2323
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug ezycom.retroswim.net 2323
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=ezycom.retroswim.net port=2323
INFO client_base.py:188 Connected to <Peer 103.95.113.91 2323>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:789 WILL ECHO unsolicited
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC DONT ECHO
DEBUG stream_writer.py:2010 handle_dont(ECHO)
DEBUG stream_writer.py:3384 pending_option[WILL + ECHO] = False
DEBUG stream_writer.py:3384 local_option[ECHO] = False
DEBUG stream_writer.py:773 recv IAC WILL BINARY
DEBUG stream_writer.py:789 WILL BINARY unsolicited
DEBUG stream_writer.py:2045 handle_will(BINARY)
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 remote_option[BINARY] = True
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = False
DEBUG stream_writer.py:773 recv IAC DO BINARY
DEBUG stream_writer.py:1887 handle_do(BINARY)
DEBUG stream_writer.py:3384 pending_option[WILL + BINARY] = True
DEBUG stream_writer.py:1024 send IAC WILL BINARY
DEBUG stream_writer.py:3384 local_option[BINARY] = True
DEBUG stream_writer.py:3384 pending_option[WILL + BINARY] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:789 WILL SGA unsolicited
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DO SGA
DEBUG stream_writer.py:1887 handle_do(SGA)
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = True
DEBUG stream_writer.py:1024 send IAC WILL SGA
DEBUG stream_writer.py:3384 local_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[WILL + SGA] = False
DEBUG stream_writer.py:773 recv IAC DONT ZMP
DEBUG stream_writer.py:2010 handle_dont(ZMP)
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = False
DEBUG stream_writer.py:3384 local_option[ZMP] = False
DEBUG stream_writer.py:773 recv IAC DONT AARDWOLF
DEBUG stream_writer.py:2010 handle_dont(AARDWOLF)
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = False
DEBUG stream_writer.py:3384 local_option[AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC DONT MSDP
DEBUG stream_writer.py:2010 handle_dont(MSDP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = False
DEBUG stream_writer.py:3384 local_option[MSDP] = False
DEBUG stream_writer.py:773 recv IAC DONT GMCP
DEBUG stream_writer.py:2010 handle_dont(GMCP)
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = False
DEBUG stream_writer.py:3384 local_option[GMCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MXP
DEBUG stream_writer.py:2010 handle_dont(MXP)
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = False
DEBUG stream_writer.py:3384 local_option[MXP] = False
DEBUG stream_writer.py:773 recv IAC DONT ATCP
DEBUG stream_writer.py:2010 handle_dont(ATCP)
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = False
DEBUG stream_writer.py:3384 local_option[ATCP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSSP
DEBUG stream_writer.py:2010 handle_dont(MSSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = False
DEBUG stream_writer.py:3384 local_option[MSSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MSP
DEBUG stream_writer.py:2010 handle_dont(MSP)
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = False
DEBUG stream_writer.py:3384 local_option[MSP] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP2_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC DONT MCCP3_COMPRESS
DEBUG stream_writer.py:2010 handle_dont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 local_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT ZMP
DEBUG stream_writer.py:2199 handle_wont(ZMP)
DEBUG stream_writer.py:3384 remote_option[ZMP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = False
DEBUG stream_writer.py:773 recv IAC WONT AARDWOLF
DEBUG stream_writer.py:2199 handle_wont(AARDWOLF)
DEBUG stream_writer.py:3384 remote_option[AARDWOLF] = False
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = False
DEBUG stream_writer.py:773 recv IAC WONT MSDP
DEBUG stream_writer.py:2199 handle_wont(MSDP)
DEBUG stream_writer.py:3384 remote_option[MSDP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = False
DEBUG stream_writer.py:773 recv IAC WONT GMCP
DEBUG stream_writer.py:2199 handle_wont(GMCP)
DEBUG stream_writer.py:3384 remote_option[GMCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MXP
DEBUG stream_writer.py:2199 handle_wont(MXP)
DEBUG stream_writer.py:3384 remote_option[MXP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = False
DEBUG stream_writer.py:773 recv IAC WONT ATCP
DEBUG stream_writer.py:2199 handle_wont(ATCP)
DEBUG stream_writer.py:3384 remote_option[ATCP] = False
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSSP
DEBUG stream_writer.py:2199 handle_wont(MSSP)
DEBUG stream_writer.py:3384 remote_option[MSSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MSP
DEBUG stream_writer.py:2199 handle_wont(MSP)
DEBUG stream_writer.py:3384 remote_option[MSP] = False
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP2_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP2_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP2_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = False
DEBUG stream_writer.py:773 recv IAC WONT MCCP3_COMPRESS
DEBUG stream_writer.py:2199 handle_wont(MCCP3_COMPRESS)
DEBUG stream_writer.py:3384 remote_option[MCCP3_COMPRESS] = False
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = False
DEBUG client_base.py:510 negotiation complete after 2.75s.
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:773 recv IAC WONT STATUS
DEBUG stream_writer.py:2199 handle_wont(STATUS)
DEBUG stream_writer.py:3384 remote_option[STATUS] = False
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = False
DEBUG stream_writer.py:773 recv IAC WONT CHARSET
DEBUG stream_writer.py:2199 handle_wont(CHARSET)
DEBUG stream_writer.py:3384 remote_option[CHARSET] = False
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = False
DEBUG stream_writer.py:773 recv IAC WONT EOR
DEBUG stream_writer.py:2199 handle_wont(EOR)
DEBUG stream_writer.py:3384 remote_option[EOR] = False
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = False
DEBUG stream_writer.py:773 recv IAC WONT COM_PORT_OPTION
DEBUG stream_writer.py:2199 handle_wont(COM_PORT_OPTION)
DEBUG stream_writer.py:3384 remote_option[COM_PORT_OPTION] = False
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = False
DEBUG fingerprinting.py:844 connection for server fingerprint db901ebd131f6da3
INFO client_base.py:120 Connection closed to <Peer 103.95.113.91 2323>