dcastle.org:6666
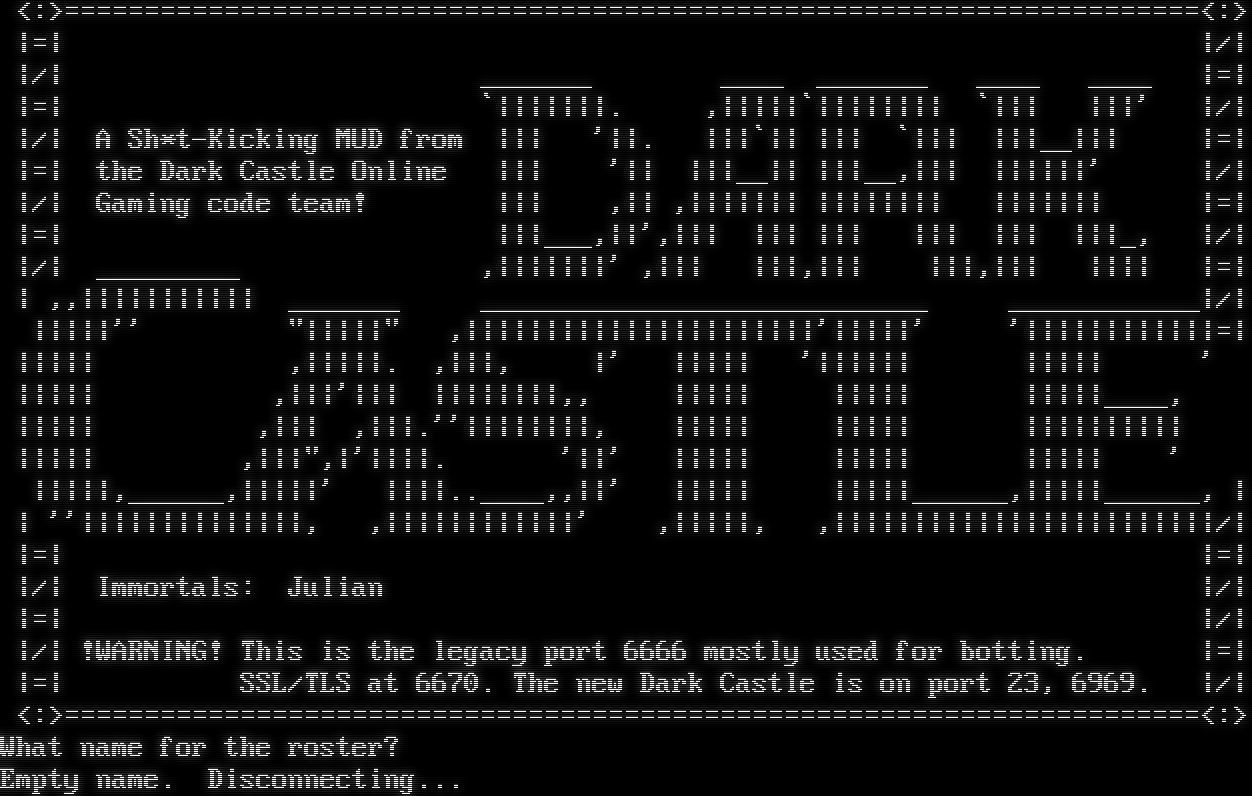
Connection Banner:
Server URLs
Server Location: 🇺🇸 United States (GeoIP)
Encoding
Effective encoding: ascii
Scanner detected: cp437
Telnet Fingerprint
This fingerprint is shared by 40 other servers.
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "c2dd7d4e76383b41",
"fingerprint-data": {
"offered-options": [],
"probed-protocol": "server",
"refused-options": [],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "Empty name. Disconnecting...",
"banner_before_return": "\r\n Inspiration from: M.Seifert, H.Staerfeldt, S.Hammer, T.Madsen, K.Nyboe\n\r <:>=======================================================================<:>\n\r |=| |/|\n\r |/| _______ ____ _______ ____ ____ |=|\n\r |=| `|||||||. ,|||||`|||||||| `||| |||' |/|\n\r |/| A Sh*t-Kicking MUD from ||| '||. |||`|| ||| `||| |||__||| |=|\n\r |=| the Dark Castle Online ||| '|| |||__|| |||__,||| ||||||' |/|\n\r |/| Gaming code team! ||| ,|| ,||||||| |||||||| ||||||| |=|\n\r |=| |||___,||',||| ||| ||| ||| ||| |||_, |/|\n\r |/| _________ ,|||||||' ,||| |||,||| |||,||| |||| |=|\n\r | ,,||||||||||| _______ ____________________________ ____________|/|\n\r |||||'' \"|||||\" ,||||||||||||||||||||||'|||||' '||||||||||||=|\n\r ||||| ,|||||. ,|||, |' ||||| '|||||| ||||| ' \n\r ||||| ,|||'||| ||||||||,, ||||| ||||| |||||____, \n\r ||||| ,||| ,|||.''||||||||, ||||| ||||| |||||||||| \n\r ||||| ,|||\",|'||||. '||' ||||| ||||| ||||| ' \n\r |||||,______,|||||' ||||..____,,||' ||||| |||||______,|||||______, |\n\r | ''||||||||||||||, ,||||||||||||' ,|||||, ,||||||||||||||||||||||||/|\n\r |=| |=|\n\r |/| Immortals: Julian |/|\n\r |=| |/|\n\r |/| !WARNING! This is the legacy port 6666 mostly used for botting. |=|\n\r |=| SSL/TLS at 6670. The new Dark Castle is on port 23, 6969. |/|\n\r <:>=======================================================================<:>\n\rWhat name for the roster? ",
"dsr_replies": 0,
"dsr_requests": 0,
"encoding": "cp437",
"option_states": {
"server_offered": {},
"server_requested": {}
},
"scan_type": "quick",
"timing": {
"probe": 0.0,
"total": 5.633126258850098
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:19:45.581340+00:00",
"host": "dcastle.org",
"ip": "72.14.179.114",
"port": 6666
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug dcastle.org 6666
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=dcastle.org port=6666
INFO client_base.py:186 Connected to <Peer 72.14.179.114 6666>
DEBUG stream_writer.py:3330 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1019 send IAC WILL MXP
DEBUG stream_writer.py:3330 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1019 send IAC WILL ATCP
DEBUG stream_writer.py:3330 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1019 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3330 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1019 send IAC WILL GMCP
DEBUG stream_writer.py:3330 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1019 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3330 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1019 send IAC WILL MSP
DEBUG stream_writer.py:3330 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1019 send IAC WILL MSDP
DEBUG stream_writer.py:3330 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1019 send IAC WILL MSSP
DEBUG stream_writer.py:3330 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1019 send IAC WILL ZMP
DEBUG stream_writer.py:3330 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1019 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3330 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1019 send IAC DO MXP
DEBUG stream_writer.py:3330 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1019 send IAC DO ATCP
DEBUG stream_writer.py:3330 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1019 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:3330 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1019 send IAC DO GMCP
DEBUG stream_writer.py:3330 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1019 send IAC DO AARDWOLF
DEBUG stream_writer.py:3330 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1019 send IAC DO MSP
DEBUG stream_writer.py:3330 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1019 send IAC DO MSDP
DEBUG stream_writer.py:3330 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1019 send IAC DO MSSP
DEBUG stream_writer.py:3330 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1019 send IAC DO ZMP
DEBUG stream_writer.py:3330 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1019 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:1400 IAC GA: Go-Ahead (unhandled).
DEBUG client_base.py:499 negotiation failed after 4.01s.
DEBUG client_base.py:505 failed-reply: 'WILL MXP, WILL ATCP, WILL MCCP3_COMPRESS, WILL GMCP, WILL AARDWOLF, WILL MSP, WILL MSDP,
WILL MSSP, WILL ZMP, WILL MCCP2_COMPRESS, DO MXP, DO ATCP, DO MCCP3_COMPRESS, DO GMCP, DO AARDWOLF, DO MSP, DO MSDP, DO MSSP,
DO ZMP, DO MCCP2_COMPRESS'
DEBUG client_base.py:89 EOF from server, closing.
INFO client_base.py:118 Connection closed to <Peer 72.14.179.114 6666>
INFO fingerprinting.py:755 connection for server fingerprint c2dd7d4e76383b41