bbs.outpost9.co:2023
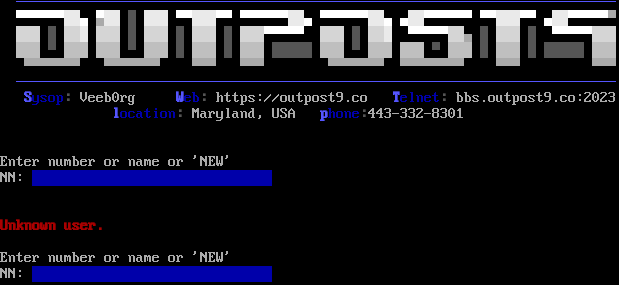
Connection Banner:
Server URLs
- Telnet: bbs.outpost9.co:2023
- Website: http://outpost9.co
Server Location: 🇺🇸 United States (GeoIP)
Listing
BBS Name: Outpost 9 (BBS) (from listing)
Sysop: Veeb0rg
Listed Location: Glen Burnie, MD, USA
BBS Software
Detected: WWIV
Encoding
Effective encoding: cp437
Override: cp437 (from bbslist.txt)
Scanner detected: cp437
Telnet Fingerprint
This fingerprint is shared by 36 other servers.
Options offered by server: ECHO, SGA
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "4305c7e02be02e5d",
"fingerprint-data": {
"offered-options": [
"ECHO",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"BINARY",
"CHARSET",
"COM_PORT",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[0;37;40m\r\n\r\n\u001b[0;31;40;1mUnknown user.\r\u001b[0;37;40m\n\r\nEnter number or name or 'NEW'\r\nNN: \u001b[s\u001b[0;37;44;1m \u001b[u\u001b[s\u001b[u\u001b[s\u001b[u\u001b[s",
"banner_before_return": "Client Address: modem.xyz (143.198.61.53)\r\n\r\n\r\nWWIV 5.8.1.3688\r\nCopyright (c) 1998-2023, WWIV Software Services.\r\nAll Rights Reserved.\r\n\u001b[s\u001b[999;999H\u001b[6n\u001b[u\u001b[6n\r\n\u001b[?7h\u001b[40m\u001b[2J\u001b[40m\r\n\u001b[0;1m \u001b[34m\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\r\n \u001b[37m\u2580\u2580\u2580\u2580\u2580\u2580\u001b[47m\u2593\u2593\u001b[40m\u2584 \u001b[47m\u2580\u2593\u2593\u001b[1C\u001b[30;40m\u2588 \u001b[37;47m\u2593\u2593\u2593\u001b[1C\u001b[40m\u2580\u2580\u001b[47m\u2593\u2593\u2593\u001b[40m\u2580\u2580 \u2580\u2580\u2580\u2580\u2580\u2580\u001b[47m\u2593\u2593\u001b[40m\u2584 \u2580\u2580\u2580\u2580\u2580\u2580\u001b[47m\u2593\u2593\u001b[40m\u2584 \u2584\u001b[47m\u2593\u2593\u001b[40m\u2580\u2580\u2580\u2580\u2580\u2580 \u2580\u2580\u001b[47m\u2593\u2593\u2593\u001b[40m\u2580\u2580 \u2584\u001b[47m\u2593\u2593\u001b[40m\u2580\u2580\u2580\u2580\u2580\u001b[0m\u2580\r\n \u001b[1;47m\u2592\u2592\u2592\u001b[1C\u001b[30;40m\u2588 \u001b[37;47m\u2592\u2592\u2593\u001b[1C\u2592\u2592\u2592\u001b[1C\u001b[30;40m\u2588 \u001b[37;47m\u2592\u2592\u2592\u001b[1C\u001b[30;40m\u2588 \u001b[37;47m\u2592\u2592\u2592\u001b[1C\u001b[30;40m\u2588 \u001b[37;47m\u2592\u2592\u2592\u001b[40m\u2580\u2580\u2580\u2580\u2580 \u001b[47m\u2592\u2592\u2592\u001b[1C\u001b[30;40m\u2588 \u001b[37;47m\u2592\u2592\u2593\u001b[2C\u001b[40m\u2580\u2580\u2580\u2580\u2580\u001b[47m\u2592\u2592\u001b[0m\u2584 \u001b[1;30m\u2588 \u001b[37;47m\u2592\u2592\u2592\u001b[1C\u001b[30;40m\u2588 \u001b[37m\u2580\u2580\u2580\u2580\u2580\u001b[47m\u2592\u2592\u2592\u001b[40m\r\n \u001b[47m\u2591\u2591\u2591\u001b[1C\u001b[30;40m\u2580 \u001b[37;47m\u2591\u2591\u2591\u001b[1C\u2591\u2591\u2591\u001b[1C\u001b[30;40m\u2580 \u001b[37;47m\u2591\u2591\u2591\u001b[1C\u001b[30;40m\u2588 \u001b[37;47m\u2591\u2591\u2591\u001b[1C\u001b[30;40m\u2588 \u001b[37;47m\u2591\u2591\u2591\u001b[1C\u001b[30;40m\u2588\u2588\u2588\u2588\u2588 \u001b[37;47m\u2591\u2591\u2591\u001b[1C\u001b[30;40m\u2580 \u001b[37;47m\u2591\u2591\u2591\u001b[1C\u2591\u2591\u2591\u001b[1C\u001b[30;40m\u2580 \u001b[37;47m\u2591\u2591\u2591\u001b[1C\u001b[30;40m\u2588 \u001b[37;47m\u2591\u2591\u2591\u001b[1C\u001b[30;40m\u2588 \u2588\u2588\u2588\u2588\u2588 \u001b[37;47m\u2591\u2591\u2591\u001b[40m\r\n \u001b[0m\u2580\u2580\u2580\u2580\u2580\u2580\u2580 \u2580\u2580\u2580\u2580\u2580\u2580\u2580 \u2580\u2580\u2580 \u2580\u2580\u2580\u001b[8C\u2580\u2580\u2580\u2580\u2580\u2580\u2580 \u2580\u2580\u2580\u2580\u2580\u2580\u2580\u2580 \u2580\u2580\u2580\u001b[9C\u2580\u2580\u2580\r\n \u001b[1;34m\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\r\n S\u001b[0;34mysop\u001b[1;30m: \u001b[0mVeeb0rg\u001b[5C\u001b[1;34mW\u001b[0;34meb\u001b[1;30m: \u001b[0mhttps://outpost9.co \u001b[1;34mT\u001b[0;34melnet\u001b[1;30m: \u001b[0mbbs.outpost9.co:2023\r\n\u001b[14C\u001b[1;34ml\u001b[0;34mocation\u001b[1;30m: \u001b[0mMaryland, USA \u001b[1;34mp\u001b[0;34mhone\u001b[1;30m:\u001b[0m443-332-8301\r\n\u001b[0m\u001b[255D\r\n\r\nEnter number or name or 'NEW'\r\nNN: \u001b[s\u001b[0;37;44;1m \u001b[u\u001b[s\u001b[u\u001b[s",
"dsr_replies": 2,
"dsr_requests": 2,
"encoding": "cp437",
"option_states": {
"server_offered": {
"ECHO": true,
"SGA": true
},
"server_requested": {
"ECHO": false,
"LINEMODE": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.5125541687011719,
"total": 11.154021501541138
}
}
},
"sessions": [
{
"connected": "2026-03-07T04:13:25.533528+00:00",
"host": "bbs.outpost9.co",
"ip": "68.134.179.115",
"port": 2023
},
{
"connected": "2026-04-05T18:35:24.829739+00:00",
"host": "bbs.outpost9.co",
"ip": "68.134.179.115",
"port": 2023
},
{
"connected": "2026-04-07T05:39:16.978810+00:00",
"host": "bbs.outpost9.co",
"ip": "68.134.179.115",
"port": 2023
},
{
"connected": "2026-04-08T17:09:32.375298+00:00",
"host": "bbs.outpost9.co",
"ip": "68.134.179.115",
"port": 2023
},
{
"connected": "2026-04-10T00:32:23.936831+00:00",
"host": "bbs.outpost9.co",
"ip": "68.134.179.115",
"port": 2023
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug bbs.outpost9.co 2023
Show Logfile
DEBUG client.py:1193 Fingerprint client: host=bbs.outpost9.co port=2023
INFO client_base.py:188 Connected to <Peer 68.134.179.115 2023>
DEBUG stream_writer.py:3384 pending_option[WILL + ZMP] = True
DEBUG stream_writer.py:1024 send IAC WILL ZMP
DEBUG stream_writer.py:3384 pending_option[WILL + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC WILL AARDWOLF
DEBUG stream_writer.py:3384 pending_option[WILL + MSDP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSDP
DEBUG stream_writer.py:3384 pending_option[WILL + GMCP] = True
DEBUG stream_writer.py:1024 send IAC WILL GMCP
DEBUG stream_writer.py:3384 pending_option[WILL + MXP] = True
DEBUG stream_writer.py:1024 send IAC WILL MXP
DEBUG stream_writer.py:3384 pending_option[WILL + ATCP] = True
DEBUG stream_writer.py:1024 send IAC WILL ATCP
DEBUG stream_writer.py:3384 pending_option[WILL + MSSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSSP
DEBUG stream_writer.py:3384 pending_option[WILL + MSP] = True
DEBUG stream_writer.py:1024 send IAC WILL MSP
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[WILL + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC WILL MCCP3_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + ZMP] = True
DEBUG stream_writer.py:1024 send IAC DO ZMP
DEBUG stream_writer.py:3384 pending_option[DO + AARDWOLF] = True
DEBUG stream_writer.py:1024 send IAC DO AARDWOLF
DEBUG stream_writer.py:3384 pending_option[DO + MSDP] = True
DEBUG stream_writer.py:1024 send IAC DO MSDP
DEBUG stream_writer.py:3384 pending_option[DO + GMCP] = True
DEBUG stream_writer.py:1024 send IAC DO GMCP
DEBUG stream_writer.py:3384 pending_option[DO + MXP] = True
DEBUG stream_writer.py:1024 send IAC DO MXP
DEBUG stream_writer.py:3384 pending_option[DO + ATCP] = True
DEBUG stream_writer.py:1024 send IAC DO ATCP
DEBUG stream_writer.py:3384 pending_option[DO + MSSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSSP
DEBUG stream_writer.py:3384 pending_option[DO + MSP] = True
DEBUG stream_writer.py:1024 send IAC DO MSP
DEBUG stream_writer.py:3384 pending_option[DO + MCCP2_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP2_COMPRESS
DEBUG stream_writer.py:3384 pending_option[DO + MCCP3_COMPRESS] = True
DEBUG stream_writer.py:1024 send IAC DO MCCP3_COMPRESS
DEBUG stream_writer.py:773 recv IAC DONT ECHO
DEBUG stream_writer.py:2010 handle_dont(ECHO)
DEBUG stream_writer.py:3384 pending_option[WILL + ECHO] = False
DEBUG stream_writer.py:3384 local_option[ECHO] = False
DEBUG stream_writer.py:773 recv IAC WILL ECHO
DEBUG stream_writer.py:789 WILL ECHO unsolicited
DEBUG stream_writer.py:2045 handle_will(ECHO)
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = True
DEBUG stream_writer.py:1024 send IAC DO ECHO
DEBUG stream_writer.py:3384 remote_option[ECHO] = True
DEBUG stream_writer.py:3384 pending_option[DO + ECHO] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:789 WILL SGA unsolicited
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = True
DEBUG stream_writer.py:1024 send IAC DO SGA
DEBUG stream_writer.py:3384 remote_option[SGA] = True
DEBUG stream_writer.py:3384 pending_option[DO + SGA] = False
DEBUG stream_writer.py:773 recv IAC DONT LINEMODE
DEBUG stream_writer.py:2010 handle_dont(LINEMODE)
DEBUG stream_writer.py:3384 pending_option[WILL + LINEMODE] = False
DEBUG stream_writer.py:3384 local_option[LINEMODE] = False
DEBUG stream_writer.py:773 recv IAC WILL SGA
DEBUG stream_writer.py:789 WILL SGA unsolicited
DEBUG stream_writer.py:2045 handle_will(SGA)
DEBUG client_base.py:513 negotiation failed after 4.00s.
DEBUG client_base.py:519 failed-reply: 'WILL ZMP, WILL AARDWOLF, WILL MSDP, WILL GMCP, WILL MXP, WILL ATCP, WILL MSSP, WILL MSP,
WILL MCCP2_COMPRESS, WILL MCCP3_COMPRESS, DO ZMP, DO AARDWOLF, DO MSDP, DO GMCP, DO MXP, DO ATCP, DO MSSP, DO MSP, DO
MCCP2_COMPRESS, DO MCCP3_COMPRESS'
DEBUG stream_writer.py:3384 pending_option[DO + BINARY] = True
DEBUG stream_writer.py:1024 send IAC DO BINARY
DEBUG stream_writer.py:3384 pending_option[DO + STATUS] = True
DEBUG stream_writer.py:1024 send IAC DO STATUS
DEBUG stream_writer.py:3384 pending_option[DO + CHARSET] = True
DEBUG stream_writer.py:1024 send IAC DO CHARSET
DEBUG stream_writer.py:3384 pending_option[DO + EOR] = True
DEBUG stream_writer.py:1024 send IAC DO EOR
DEBUG stream_writer.py:3384 pending_option[DO + COM_PORT_OPTION] = True
DEBUG stream_writer.py:1024 send IAC DO COM_PORT_OPTION
DEBUG stream_writer.py:998 skip DO MCCP2_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO MCCP3_COMPRESS; pending_option = True
DEBUG stream_writer.py:998 skip DO GMCP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSDP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MSP; pending_option = True
DEBUG stream_writer.py:998 skip DO MXP; pending_option = True
DEBUG stream_writer.py:998 skip DO ZMP; pending_option = True
DEBUG stream_writer.py:998 skip DO AARDWOLF; pending_option = True
DEBUG stream_writer.py:998 skip DO ATCP; pending_option = True
DEBUG fingerprinting.py:844 connection for server fingerprint 4305c7e02be02e5d
INFO client_base.py:120 Connection closed to <Peer 68.134.179.115 2023>