69.201.1.134:23
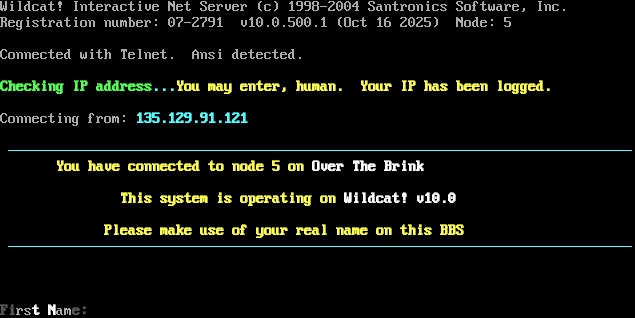
Connection Banner:
Server URLs
- Telnet: 69.201.1.134:23
- BINKP: 69.201.1.134:24554
- Website: http://69.201.1.134
Server Location: 🇺🇸 United States (GeoIP)
BBS Software
Detected: Wildcat!
Encoding
Effective encoding: cp437
Scanner detected: cp437
Telnet Fingerprint
This fingerprint is shared by 142 other servers.
Options offered by server: BINARY, ECHO, SGA
Options requested from client: BINARY
The complete JSON record collected during the scan, including Telnet negotiation results and banner data.
Show JSON
{
"server-probe": {
"fingerprint": "e9e1390d6941c201",
"fingerprint-data": {
"offered-options": [
"BINARY",
"ECHO",
"SGA"
],
"probed-protocol": "server",
"refused-options": [
"AARDWOLF",
"ATCP",
"CHARSET",
"COM_PORT",
"EOR",
"GMCP",
"MCCP2",
"MCCP3",
"MSDP",
"MSP",
"MSSP",
"MXP",
"STATUS",
"ZMP"
],
"requested-options": [
"BINARY"
],
"scan-type": "quick"
},
"session_data": {
"banner_after_return": "\u001b[0;1;40;37m",
"banner_before_return": "\f\u001b[0m\u001b[H\u001b[2J\r<WC250007-279112681D5F0FA3294823>\rWildcat! Interactive Net Server (c) 1998-2004 Santronics Software, Inc.\r\nRegistration number: 07-2791 v10.0.500.1 (Oct 16 2025) Node: 5\r\n\u001b[6n\r \r\nConnected with Telnet. Ansi detected.\r\n\r\n\u001b[0;1;40;32mChecking IP address\u001b[0;1;40;36m...\u001b[0;1;40;33mYou may enter, human. Your IP has been logged.\r\n\r\n\u001b[0;40;37mConnecting from: \u001b[0;1;40;36m135.129.91.121\r\n\r\n \u001b[0;1;40;36m\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\r\n \u001b[0;1;40;33mYou have connected to node 5 on \u001b[0;1;40;37mOver The Brink\r\n\r\n \u001b[0;1;40;33m This system is operating on \u001b[0;1;40;37mWildcat! v10.0\r\n\r\n \u001b[0;1;40;33m Please make use of your real name on this BBS\r\n \u001b[0;1;40;36m\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\u2500\r\n\r\n\r\n\r\n\u001b[0;1;40;30mFi\u001b[0;40;37mrs\u001b[0;1;40;37mt N\u001b[0;40;37mam\u001b[0;1;40;30me:\u001b[0;1;40;33m ",
"dsr_replies": 1,
"dsr_requests": 1,
"encoding": "cp437",
"option_states": {
"server_offered": {
"AARDWOLF": false,
"ATCP": false,
"BINARY": true,
"ECHO": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"SGA": true,
"ZMP": false
},
"server_requested": {
"AARDWOLF": false,
"ATCP": false,
"BINARY": true,
"GMCP": false,
"MCCP2": false,
"MCCP3": false,
"MSDP": false,
"MSP": false,
"MSSP": false,
"MXP": false,
"ZMP": false
}
},
"scan_type": "quick",
"timing": {
"probe": 0.20142483711242676,
"total": 12.717921018600464
}
}
},
"sessions": [
{
"connected": "2026-03-07T05:05:39.338992+00:00",
"host": "69.201.1.134",
"ip": "69.201.1.134",
"port": 23
}
]
}
Connection Log
Debug-level log of the Telnet negotiation session, showing each IAC (Interpret As Command) exchange between client and server.
Generated by telnetlib3-fingerprint
telnetlib3-fingerprint --loglevel=debug 69.201.1.134 23
Show Logfile
DEBUG client.py:1200 Fingerprint client: host=69.201.1.134 port=23
ERROR client.py:1318 69.201.1.134:23: TCP connection to 69.201.1.134:23 timed out after 30.0s